
K.S. Ramakrishnan
Chief Risk Officer, RAKBANK

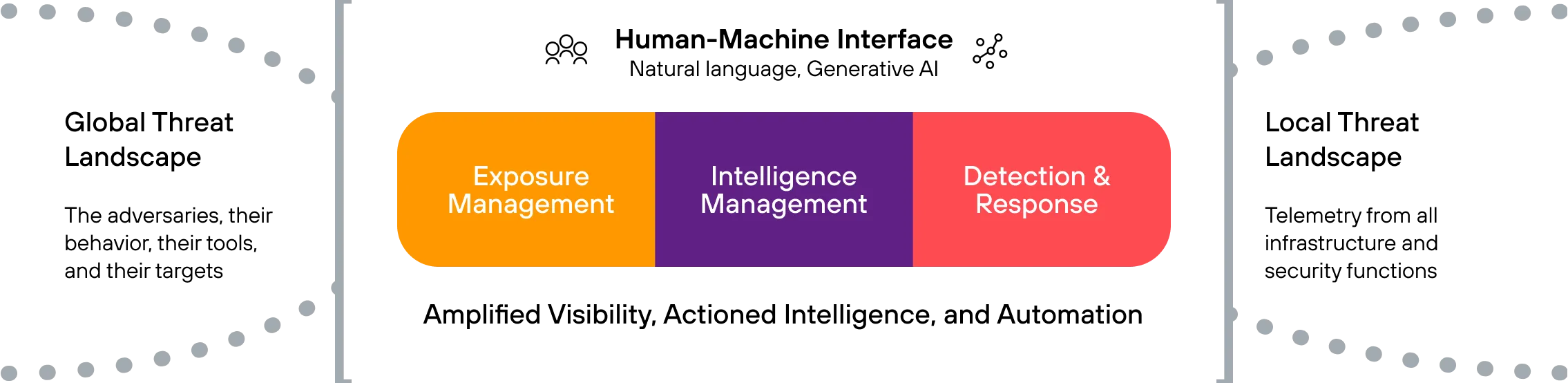
Now you can improve SOC analyst productivity, automate time-consuming tasks, and address skills shortages with one platform that combines SIEM, SOAR, and the industry’s most powerful threat intelligence capabilities.


Innovative AI that consolidates threat detection, investigation, and response into a single platform, built on the largest repository of actionable intelligence.

Improve business outcomes by enabling secure productivity. Modernize your SecOps with disruptive security analytics and AI – protect your brand, automate operations, and reduce costs.

Identify and prioritize threats with high-precision detection and enriched context. Predict the attacker’s next steps and automate your response to improve analyst efficiency and minimize impact.

Operationalize threat intelligence and advance your knowledge of the risk surface and adversary. Elevate intelligence from feeds to strategic insights that inform executive business decisions.

Know your adversary and their TTPs to predict their moves and hunt for attacker footprints in your organization. Maximize response efficacy and minimize time to respond.

Hugh Njemanze, Founder and President of Anomali, describes how organizations can apply security analytics at cloud scale, allowing them to automate workflows, detect threats and gain insights that help them power their business.










Learn how Anomali can help you cost-effectively improve your security posture.


